Finding eval(), exec(), and Insecure SQL Queries¶
Injection occurs when untrusted input is treated as code or as part of a command. In Python, this most often manifests in three ways:
Dynamic code execution (
eval,exec)Shell command execution
Unsafely constructed SQL queries
Dangerous Dynamic Execution: eval() and exec()¶
Both eval() and exec() execute strings as Python code.
user_input = input("Enter calculation: ")
result = eval(user_input)
print(result)If a user enters:
__import__("os").system("rm -rf /")There is remote command execution in this code sample!
When using Python Code Audit if this code sample is saved as ‘eval_sample.py’. Use the command:
codeaudit filescan eval_sample.pyYou see that the findings are:
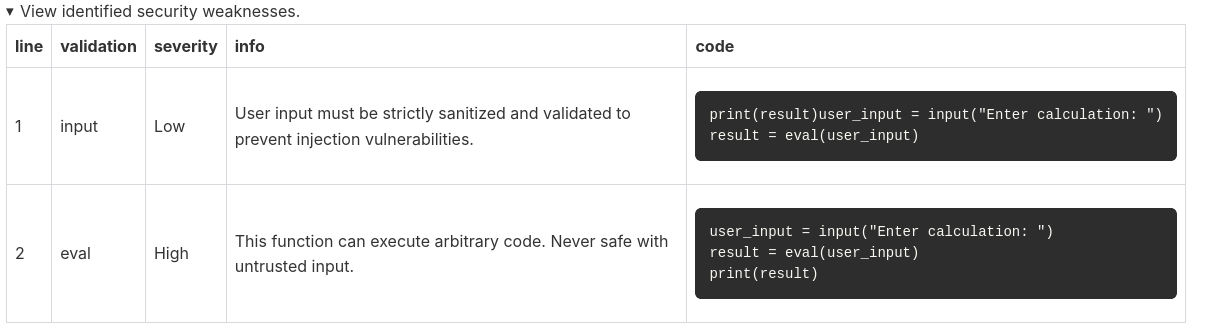
Both input and eval are detected; since both can be exploited, identifying them is essential.
This ensures that when using Python Code Audit, the detection of common injection attacks is fully supported.
What to Look for in SAST findings¶
Use of:
eval()exec()compile()input(and Any dynamic execution involving user-controlled inputTemplate engines that can be misused to execute logic
Since no SAST for Python will detect anything that might cause weakness, be alert on:
Alerts found by Python Code Audit regarding external Egress Risk.
f-strings or string concatenation passed into dangerous functions
Insecure SQL Queries¶
A common pattern in Python applications using SQLite, MySQL, or PostgreSQL:
query = f"SELECT * FROM users WHERE username = '{username}'"
cursor.execute(query)If username is:
admin' OR '1'='1The attacker bypasses authentication.
What to Look for¶
f-strings building SQL
%string formatting in queries.format()used in SQL statementsConcatenation (
+) used to construct queries
Secure Alternative¶
cursor.execute("SELECT * FROM users WHERE username = ?", (username,))Or with libraries such as SQLAlchemy, using parameterised queries or ORM query builders.
Testing Techniques¶
Fuzz input fields with:
' OR 1=1--' UNION SELECT NULL--
Use automated scanners (e.g. sqlmap) in controlled environments.
Inspect logs for malformed SQL errors.
