Introduction¶
This module focuses on structured verification techniques and the evaluation of open source software within a Python security testing context. It bridges technical testing practices with governance, assurance, and supply chain risk management.
Modern Python development relies heavily on third-party components and distributed collaboration. As a result, security testing must go beyond code-level vulnerability detection and include systematic verification, checklist-based validation, and critical evaluation of external dependencies.
By the end of this module, you will understand how to apply verification techniques effectively, use structured security baselines, and assess the security posture of open source software before integrating it into your projects.
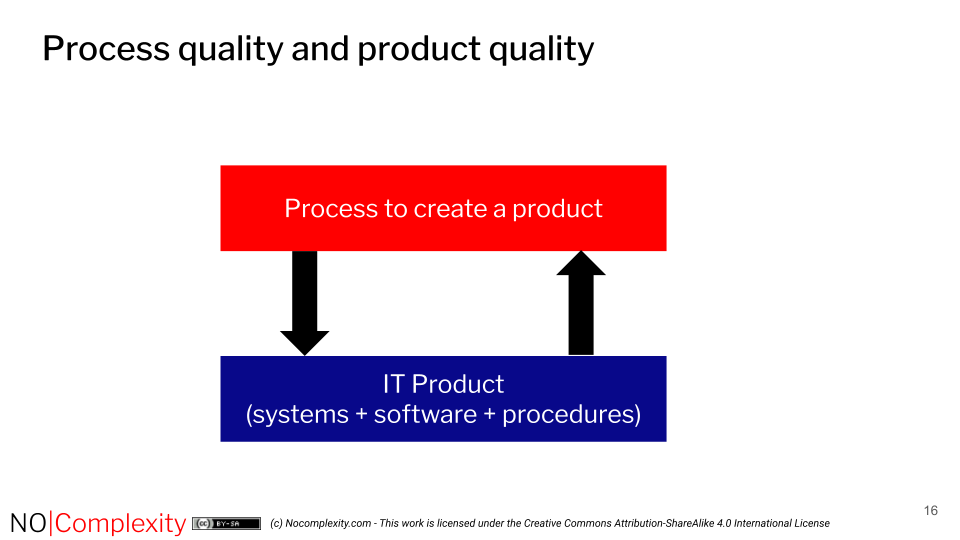
The security quality of a product is closely linked to the processes used to develop and maintain it.
Without a robust and well-defined process, achieving an acceptable level of security is largely a matter of chance. However, the reverse is also true: a product that appears secure does not necessarily indicate that the underlying development and maintenance processes meet a minimum standard of assurance.
This module consists of the following sections:
Verification Techniques: This section introduces methods for verifying security without necessarily executing the application at runtime. You will learn how to:
Why Use Checklists for Validation: In this section, you will explore why structured validation frameworks improve assurance and how they support both technical and organisational security objectives. You will learn how about:
Evaluating Open Source Software: Open source components are central to Python ecosystems. However, their adoption introduces supply chain and governance risks.
Module Outcome¶
After completing this module, you will be able to:
Apply structured verification techniques to Python projects
Use checklists and baselines to improve validation consistency
Understand the importance of reproducible builds in security assurance
Critically evaluate open source software before adoption
This module strengthens your ability to combine technical testing with governance-aware security validation — an essential capability for mastering security testing in modern Python environments.
